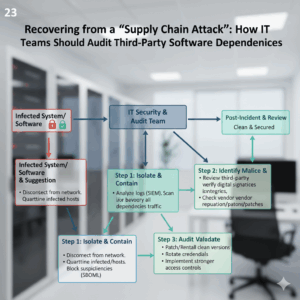
Recovering from a “Supply Chain Attack”: How IT Teams Should Audit Third-Party Software Dependencies
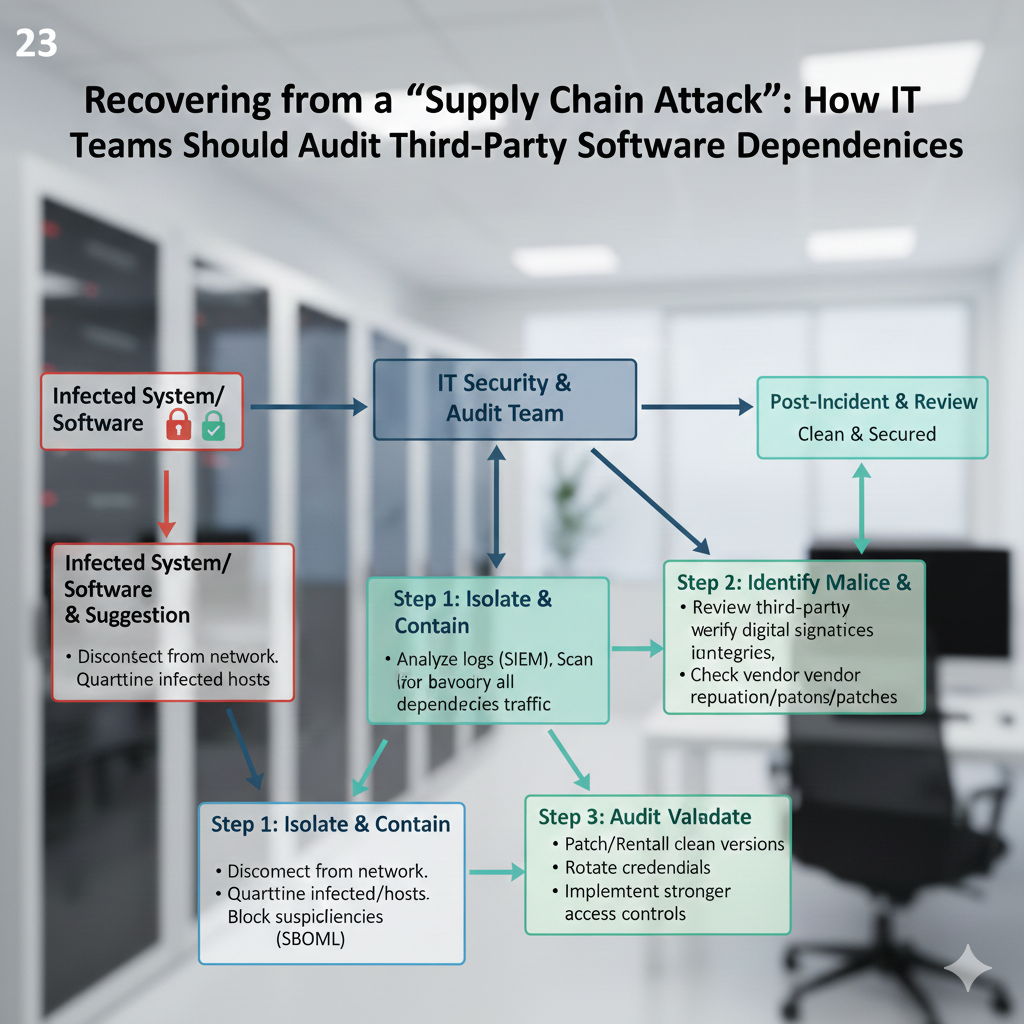
Recovering from a “Supply Chain Attack”: How IT Teams Should Audit Third-Party Software Dependencies
Attacks on supply chains have emerged as one of the most stealthy dangers that contemporary information technology settings face. In order to inject malicious code into client networks, attackers hack trusted third-party software components, libraries, or services. This allows the malware to proliferate across the client networks. An even solitary susceptible reliance has the potential to compromise security and cause disruptions in operations. Understanding the threat surface and putting in place periodic audits of third-party software are the first steps in the recovery process for information technology teams. The use of a systematic approach to auditing dependencies helps to enhance resilience, reduce risk, and guarantee that compromised components are discovered and remedied in an effective manner throughout the auditing process.
An Understanding of the Characteristics of Attacks on Supply Chains
A supply chain assault is a kind of cyberattack that targets the software or services that a business relies on, rather than directly targeting the firm itself. Libraries, package repositories, plugins, and software as a service (SaaS) applications are all potential entry points for malicious malware. Following their integration, these compromised components have the capability to steal data, establish backdoors, or carry out operations that are not permitted. since of the covert nature of these assaults, it is difficult to identify them since the software that is attacked is often thought to be trustworthy. In order to effectively recover from and avoid supply chain assaults, the first step is to identify the processes and targets of these attacks.
Creating a Map of All Dependencies on Third Parties
A thorough inventory of all third-party software that is currently being used is the first step in an effective recovery. This comprises application programming interfaces (APIs), frameworks, plugins, and software as a service (SaaS) tools. The cataloging of dependencies need to be done according to version, source, and criticality. It is possible for information technology teams to prioritize audits and remediation activities when they have a clear understanding of which components have direct access to critical systems or data. The process of mapping relationships not only offers insight into possible risk spots but also establishes a framework for continuing monitoring, which is crucial for both rapid reaction and long-term supply chain security.
Performing Code Reviews and Audits of the Security System
When conducting an audit of third-party software, it is necessary to examine the code, binaries, and update history in search of indications of compromise. For the purpose of identifying known vulnerabilities, unusual modifications, or illegal network connections, automated programs may do their scans. It is possible that a manual evaluation of crucial components will be required in order to detect less obvious modifications. Additional assurance that components are genuine is provided by the verification of cryptographic signatures and the validity of the source document. Through thorough audits, information technology teams are able to identify dependencies that have been compromised and evaluate the scale of the assault, which in turn informs the subsequent measures for containment and recovery.
Utilizing Version Control and Dependency Pinning in the Implementation
When third-party dependencies are managed correctly, the risk of being exposed to harmful updates is reduced. It is possible to guarantee that only versions of software that have been validated and tested are deployed in production by pinning them. The ability to monitor changes, roll back to known-good states, and compare updates for abnormalities is made possible by version control for information technology teams. Organizations may reduce the likelihood of automatically receiving compromised updates and increase repeatability in testing and deployment settings by exercising control over the versions of dependencies that are used.
Limiting and isolating the Effects of the Impact
After the components that have been compromised have been discovered, containment is necessary in order to stop any further spread. Disconnecting impacted systems, removing API keys, or sandboxing programs in order to restrict access are all potential steps that might be taken. Isolation immediately puts a halt to active exploitation while providing time for information technology personnel to fix and validate the integrity of systems that were not impacted. A quick containment strategy helps to reduce the amount of disturbance to operations and safeguards critical data while the recovery procedure is being carried out.
Repair and Patch Management are also included.
The remediation process includes deploying fixes, moving to alternative providers, or replacing compromised dependencies with clean versions that have been confirmed. When it comes to ensuring functionality and compatibility, IT teams are required to evaluate replacements before redeploying them. Patch management and proactive updates should be performed on a regular basis to limit the possibility of recurring exposure to vulnerabilities that are already known. Organizations are able to reestablish confidence in their software environment while simultaneously preserving operational continuity when they combine remediation with thorough testing of the program.
Making Continuous Observations and Notifications Available
It is essential to do continuous monitoring of software provided by third parties in order to forestall any future supply chain issues. It is possible for IT teams to react quickly because to the availability of tools that monitor dependency changes, validate digital signatures, and notify them of irregularities. Automated scanning and periodic audits are two methods that may assist in the early detection of new vulnerabilities or questionable activities. By ensuring that visibility is maintained across the software supply chain, defenses are strengthened and proactive intervention is made possible before assaults become more severe.
Establishing a Culture Respecting Supply Chain Security
Having a culture of security awareness is necessary for long-term resilience against assaults on supply chains. Tools alone are not enough to achieve this result. It is imperative that information technology teams work together with software developers, procurement, and management to ensure that third-party software is thoroughly vetted prior to its implementation. The best practices are formalized via the implementation of policies for vendor risk assessment, code review, and dependency management. By providing employees with training on supply chain risks and recovery procedures, an atmosphere is created in which security is emphasized. This significantly reduces the probability of a compromise occurring and ensures a prompt and efficient reaction in the event that problems develop.